Web Modelers can access the Security button, assign and customize the security settings for EPC objects if:
- They are System Admins
- They are Environment Admins
- They are an user with the Full Control Allow permission
- They are an user with the Read + Write + Delete Permission
Web Modelers need to ensure they have the permission to be a Web Modeler, the security designations above, their displayed content is set to Show Latest, and their editing tool is the Web.
The different levels of security that can be assigned to EPC objects are the following:
| Level of Security | Description |
|---|---|
| System Admin | User has all levels of permission on all objects |
| Full Control Allow | User has Write/Delete, Write, Read and Approval permissions on the object (and its children) |
| Write Delete Allow | User has Write, Read and can be granted Approval permissions on the object (and its children) |
| Write Allow | User has Read and can be granted Approval permissions on the object (and its children) |
| Read Allow | User simply has read permissions and can be granted Approval permissions on the object (and its children) |
| Show Latest Allow | User is allowed to view EPC objects in show latest |
| System Admin | Denials are overridden by System Admin Privilege, they have ultimate power on all environments and the objects within |
| Full Control Deny | User is fully denied to all EPC objects |
| Write Delete Deny | User has denied Write/Delete, they can still Read and Write on the object (and its children), and could be granted Approval permission |
| Write Deny | User has denied Write, they can still Read the object (and its children), and could be granted Approval permission. |
| Read Deny | User has been denied Read, they cannot see the object, nor be granted Approval Permission |
| Show Latest Deny | User has been denied to view EPC objects in show latest |
Object Hierarchy in EPC

EPC objects always inherit security settings from their parent object. Any change to the security settings is propagated to that object’s children. Objects inherit the cumulative permissions on the objects above them:
- For any given object, the security permissions inherited by their parent are greyed-out/disabled
The settings on child objects can be modified without affecting the settings of their parents. For lower level objects, non-inherited permissions can be granted to them. The non-inherited permissions are check-able:
- If a parent object has Allow Read permissions, the child inherits this, and could be granted Allow Write permission.
- If a parent object has Allow Read + Allow Write, the child inherits this, and could be granted Allow Write/Delete permission.
- If a parent has Deny Write/Delete permission, the child inherits this, and could be granted Deny Write.
- If a parent has Deny Write/Delete + Deny Write, the child inherits this, and could be granted Deny Read.
- For all permissions: Permissions can be further Allowed on children in this order: Read, Write, Write/Delete
- For all permissions: Permissions can be further Denied on children in this order: Write/Delete, Write, Read
Follow the instructions to set Security Permissions for an EPC Object
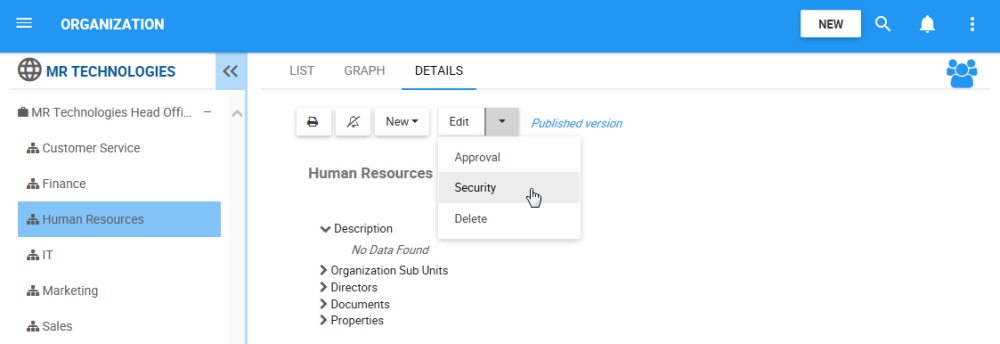
- Navigate to the details section of the object. In this example, an Organization Unit
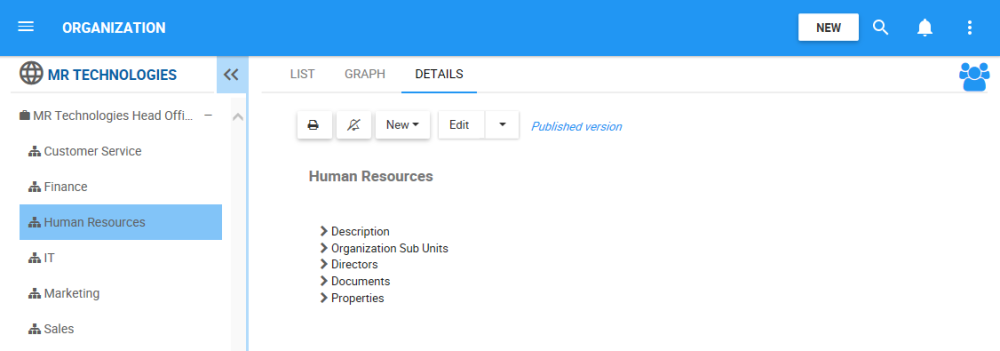
- Navigate to the
box
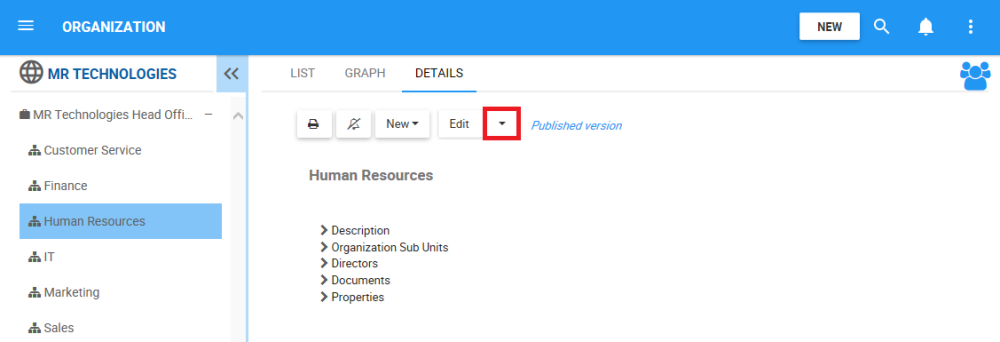
- A drop-down menu will be generated. Choose the “Security” box
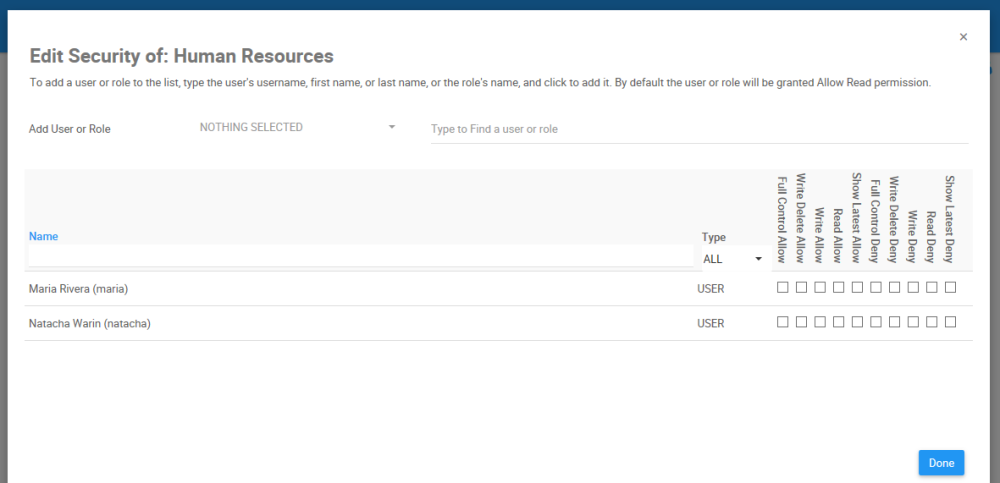
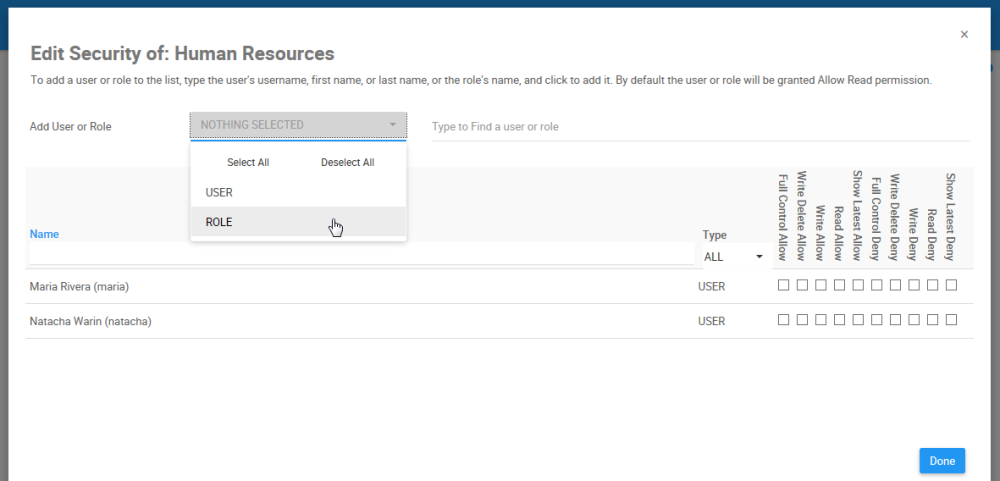
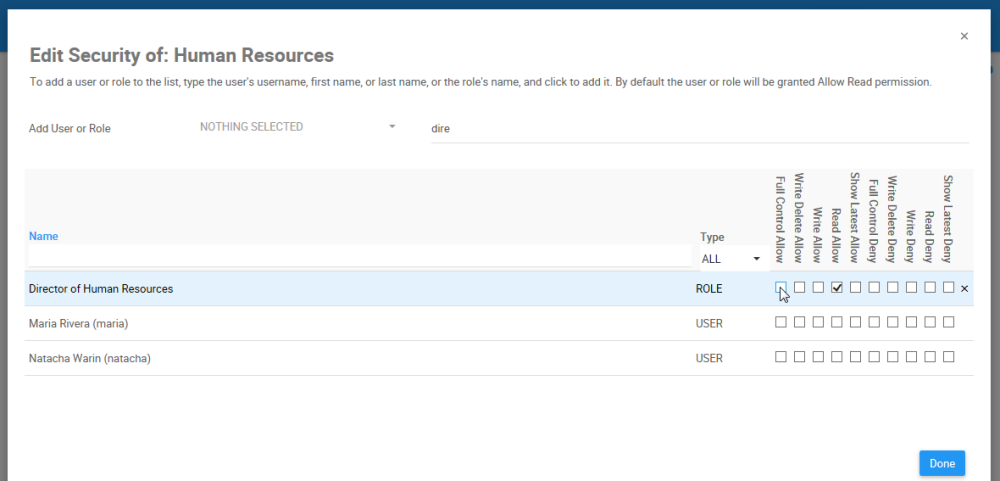
- You will be redirected to the “Edit Security of: [Object] window
- To add a user or role to the list, Navigate to “Add User or Role” and select a filter
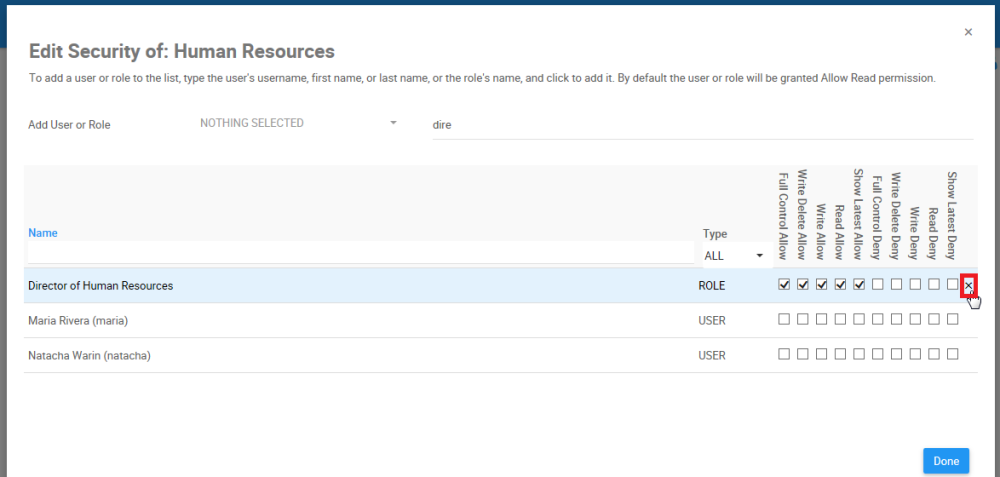
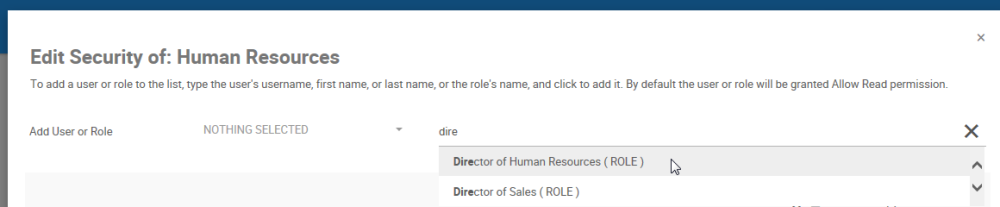
- Type the name of the Role you want to set a security permission for the EPC object. From the search suggestions, click to select the Role you want to assign
- The Role will appear on the table under, where the security level can be assigned. By default, the user or role will be granted Allow Read permission. You will receive a notification informing you the permission was added to the object.
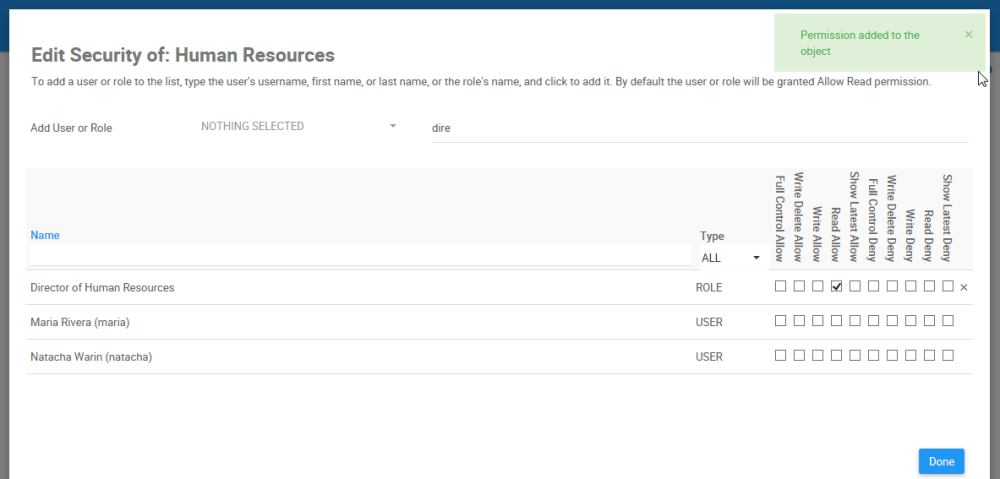
- Navigate to the “Full Control Allow” security level box for the Role
- Check to the “Full Control Allow” security level box for the Role
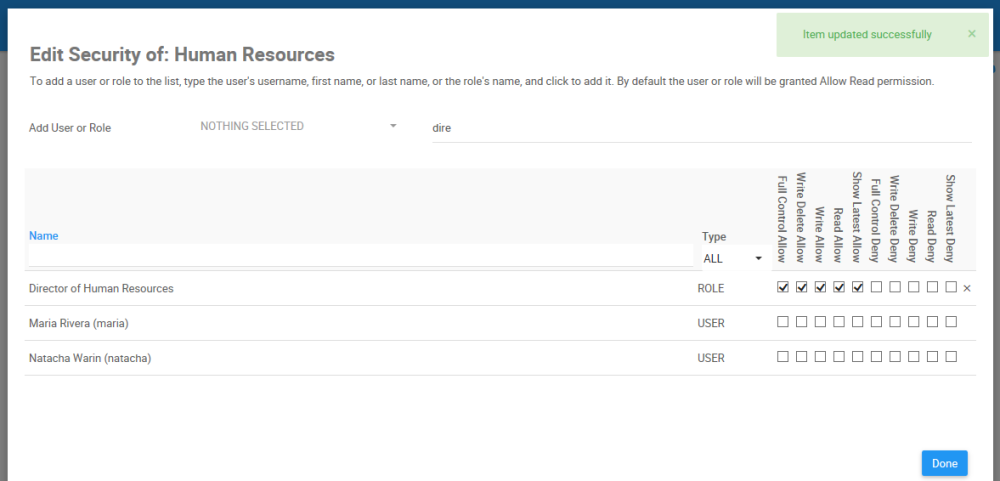
- To remove the permission from the object, click on the “x”
Haben Sie noch weitere Fragen?
Visit the Support Portal



 box
box